How Syn Flood Attack Works
The TCP SYN attack can work even on computers still compatible with very slow Internet connections. 000 Intro030 handshake237 SYN Flood Attack Backend Engineering Videoshttpswwwyoutu.
Denial Of Service Ddos Attack Geeksforgeeks
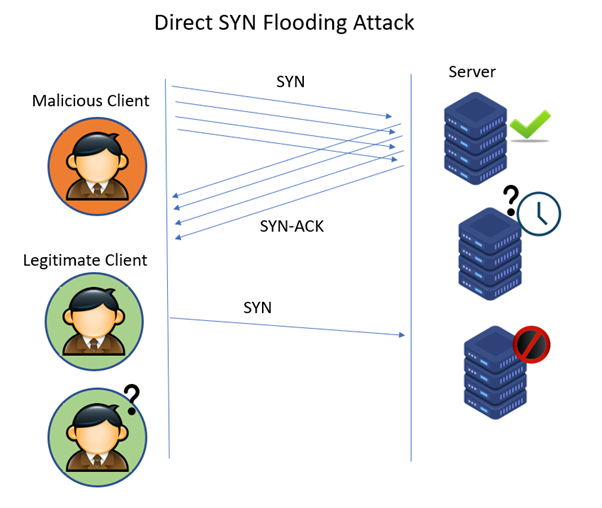
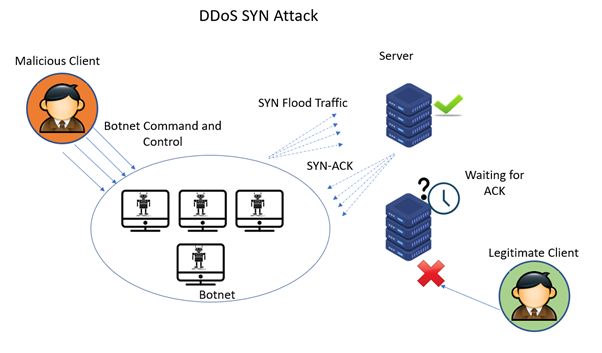
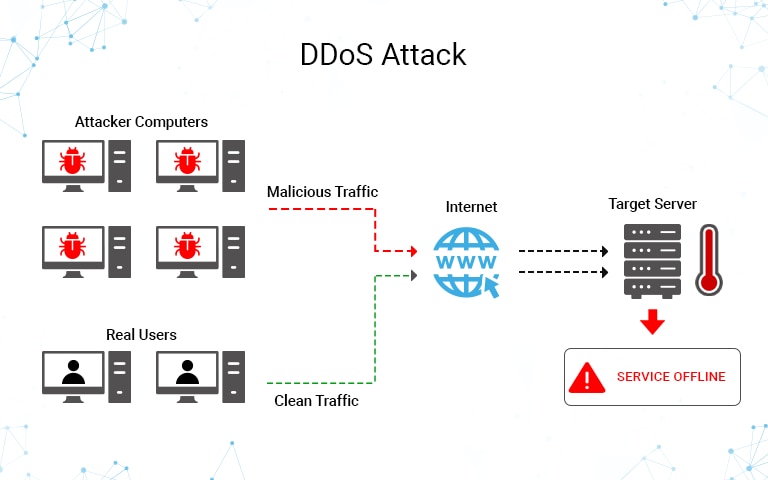
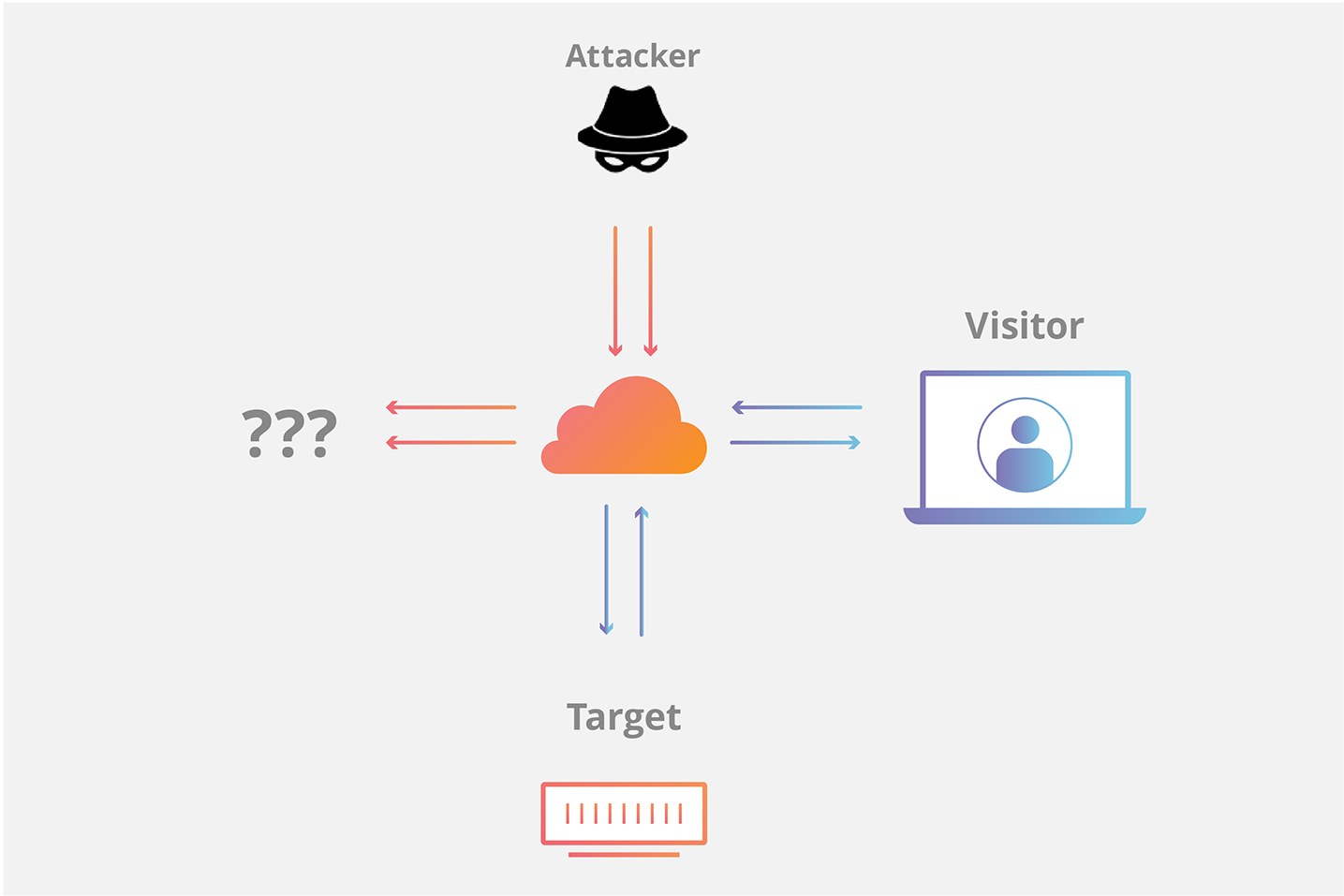
A TCP SYN flood DDoS attack occurs when the attacker floods the system with SYN requests in order to overwhelm the target and make it unable to respond to new real connection requests.
How syn flood attack works. SYN flood attacks works involve the process of exploiting the handshake process of a TCP connection. How does a SYN flood attack work. Why is a SYN Flood DDoS Attack Dangerous.
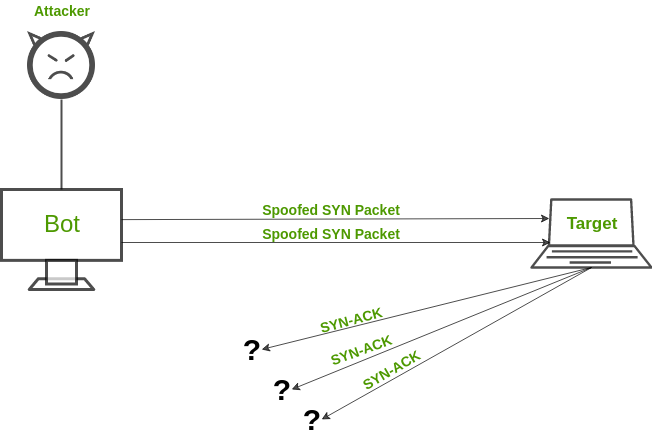
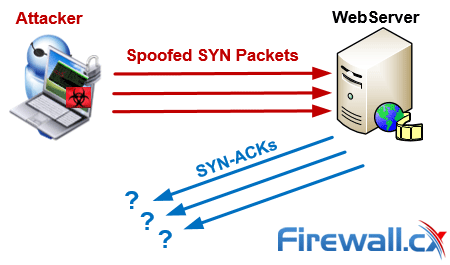
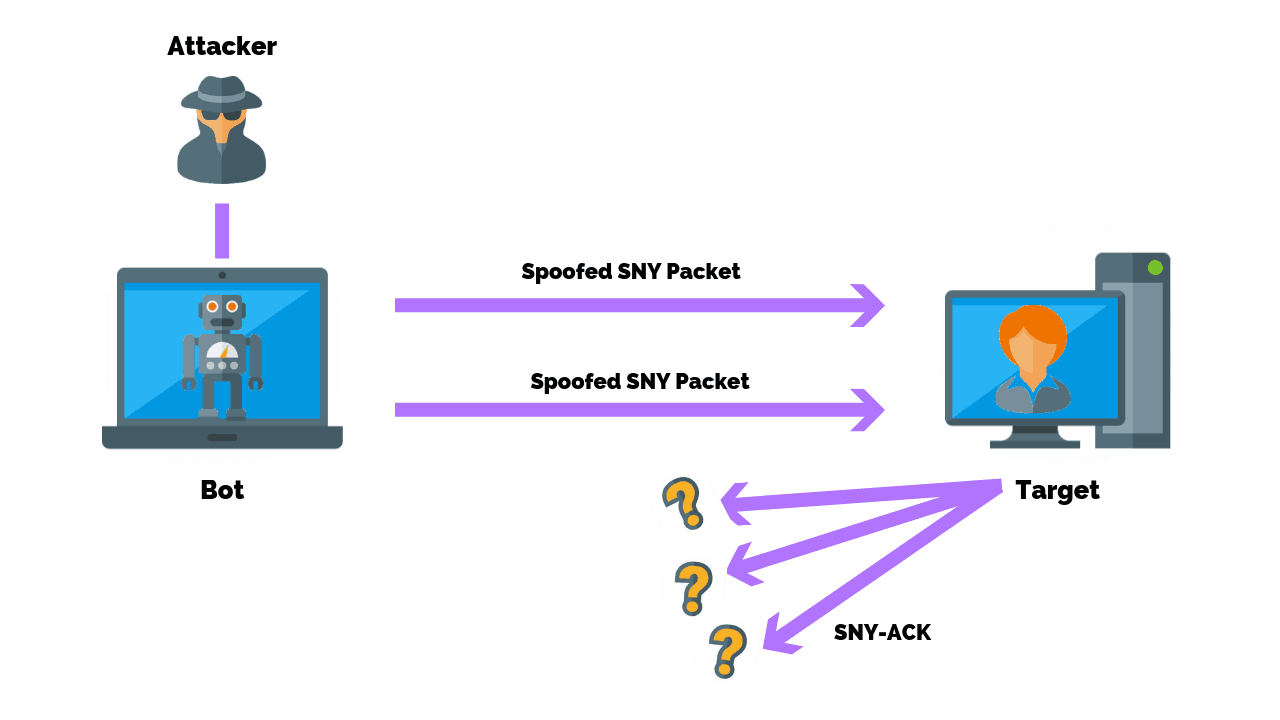
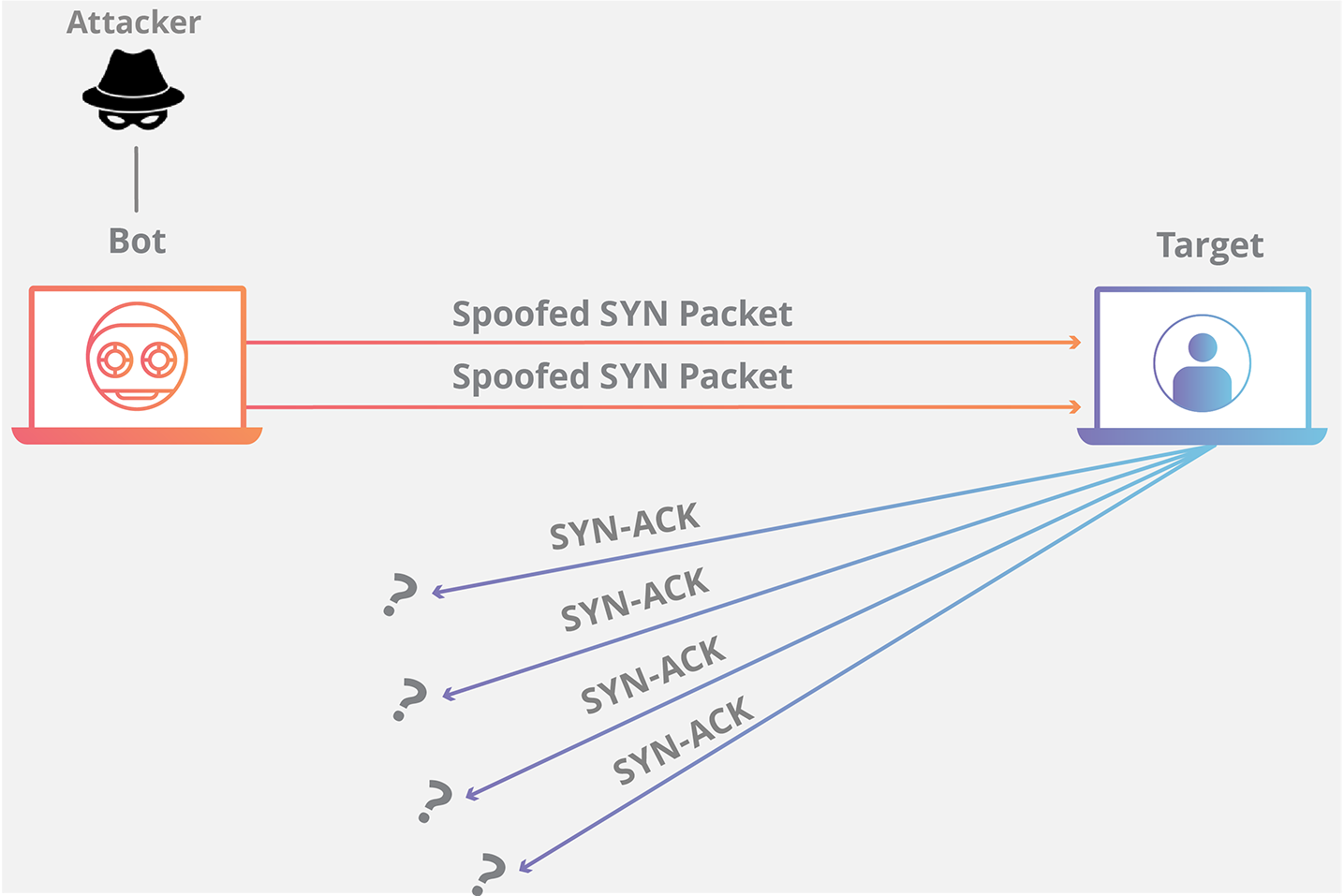
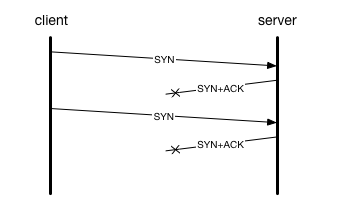
The experts from Radware have witnessed a new form of attack they consequently dubbed the Tsunami SYN flood. A SYN attack is a type of denial-of-service DoS attack in which an attacker utilizes the communication protocol of the Internet TCPIP to bombard a target system with SYN requests in an attempt to overwhelm connection queues and force a system. In a SYN flood the attacker sends a high volume of SYN packets to the server using spoofed IP addresses causing the server to send a reply SYN-ACK and leave its ports half-open awaiting for a reply from a host that doesnt exist.
A SYN flood is a DoS attack. The intent is to overload the target and stop it working as it should. Before sending the TCP RST Reset packet the sending computer first checks whether the receiving computer is actually listening for the communication or not.
It drives all of the target servers communications ports into a half-open state. A SYN packet will be sent by the client for initiating the connection. TCP SYN attacks is one of the most used DoS attacks to block a server although there are ways to mitigate it effectively.
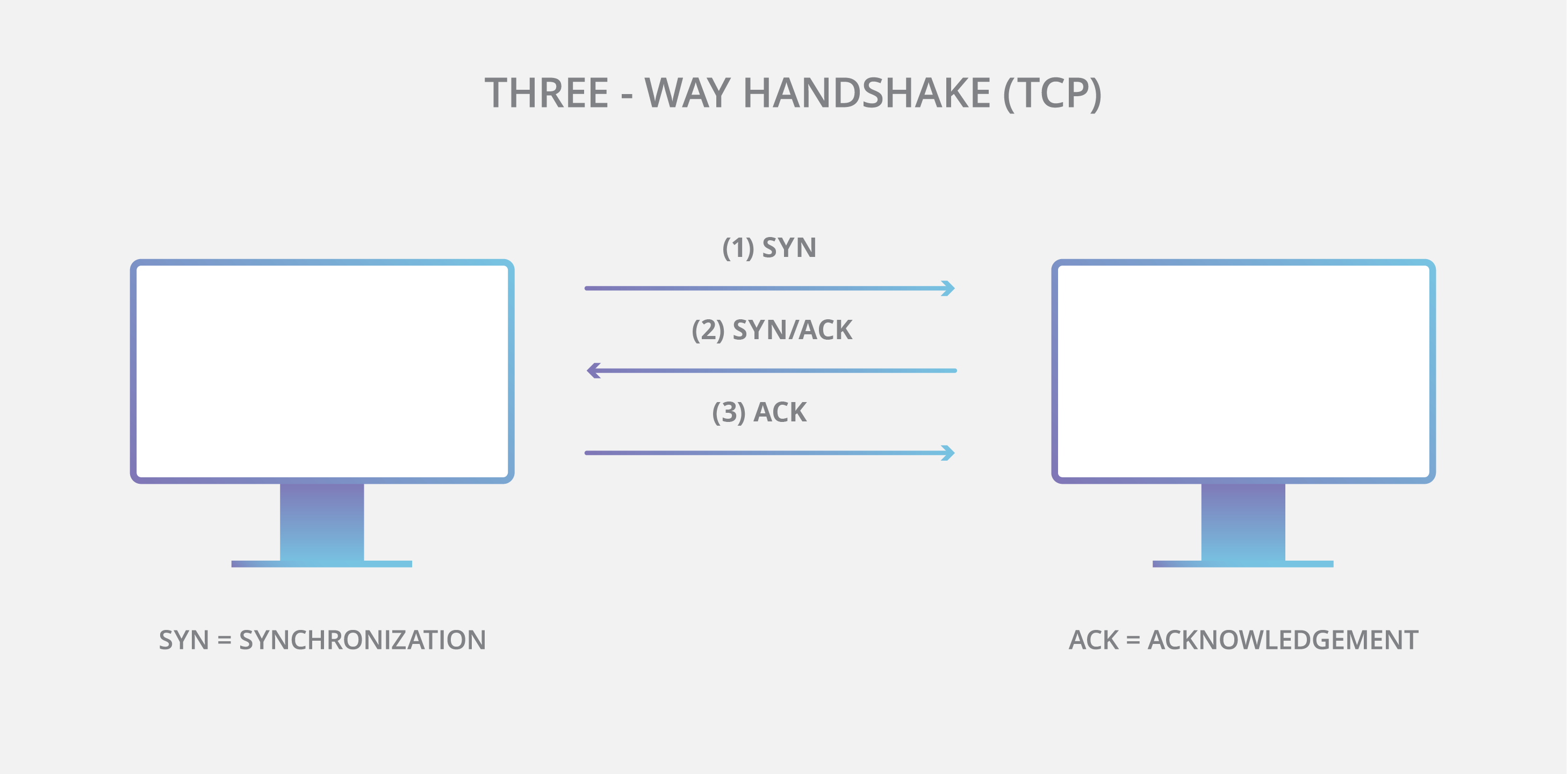
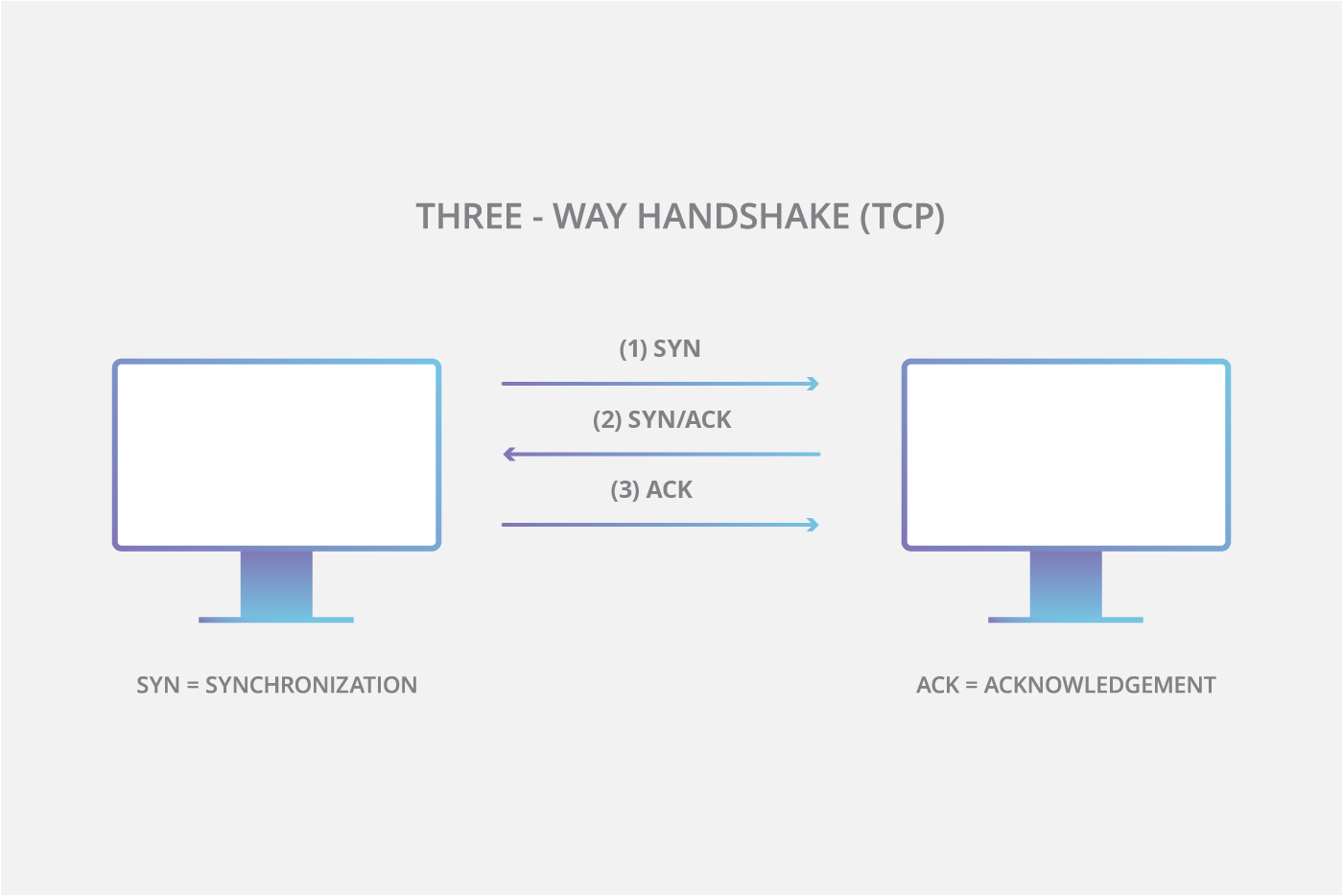
The attacker sends a flood of malicious data packets to a target system. SYN flood attacks work by exploiting the handshake process of a TCP connection. Under normal conditions a TCP connection has three distinct processes in order to make a connection.
In this video I explain how TCP SYN Flood Attack works in detail. The evildoers behind tsunami SYN flood engineered SYN packets to grow in size from their. Three distinct processes are exhibited in a TCP connection under normal conditions for establishing a connection and they are as follows.
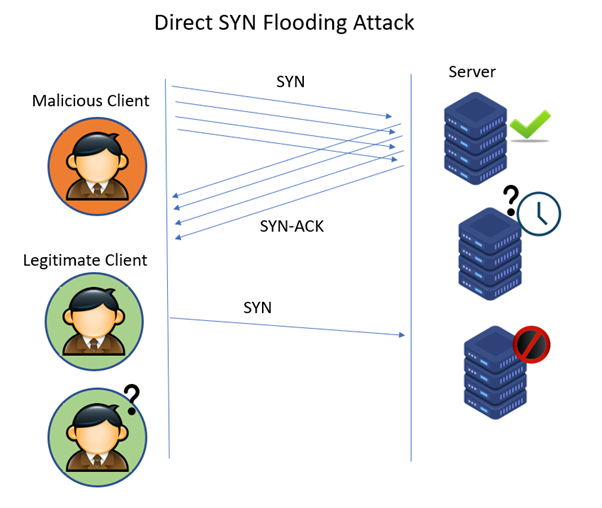
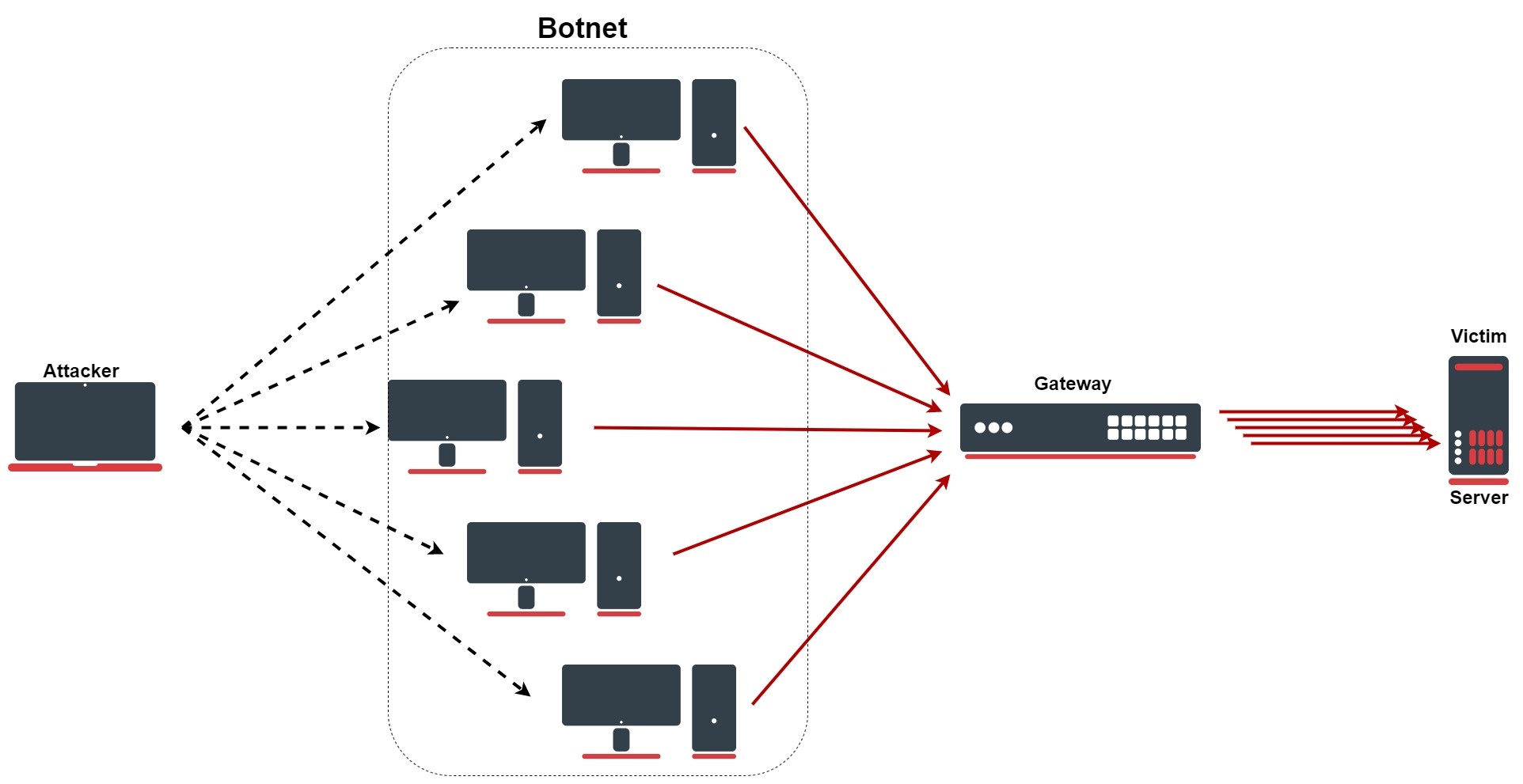
The hostile client repeatedly sends SYN synchronization packets to every port on the server using fake IP addresses. SYN flood attacks usually work by exploiting the TCP connections handshake process. Like the ping of death a SYN flood is a protocol attack.
How Syn Spoofing or TCP Reset Attack Works When a TCP connection is established between two computers the sending computer sends a TCP RST Reset packet to the receiving computer. A SYN flood is a form of denial-of-service attack in which an attacker sends a progression of SYN requests to an objectives framework trying to consume enough server assets to make the framework inert to authentic activity. First the client sends a SYN packet to the server in order to initiate the connection.
SYN attack works by flooding the victim with incomplete SYN messages. SYN flood attack also known as the half-open attack is a protocol attack which exploits the vulnerabilities in the network communication to make the victims server unavailable to. How do SYN flood attacks work.
Under normal conditions TCP connection exhibits three distinct processes in order to make a connection. Similarly to a real-world tsunami the SYN flood is huge. This is a threat that lurks both the domestic and also in the professional field of small medium and even large companies.
In this video we will thoroughly explain the SYN-Flood DDOS attackFirst we will review some TCP fundamentals followed by IP Spoofing principle and finall. First to initiate the connection the client sends an SYN packet to the server. This causes the victim machine to allocate memory resources that are never used and deny access to legitimate users.
SYN flooding is a method that the user of a hostile client program can use to conduct a denial-of-service DoS attack on a computer server.
These 6 Dns Attacks Threaten Your Business Defence Intelligence Blog

Tcp Syn Flood Attack Download Scientific Diagram
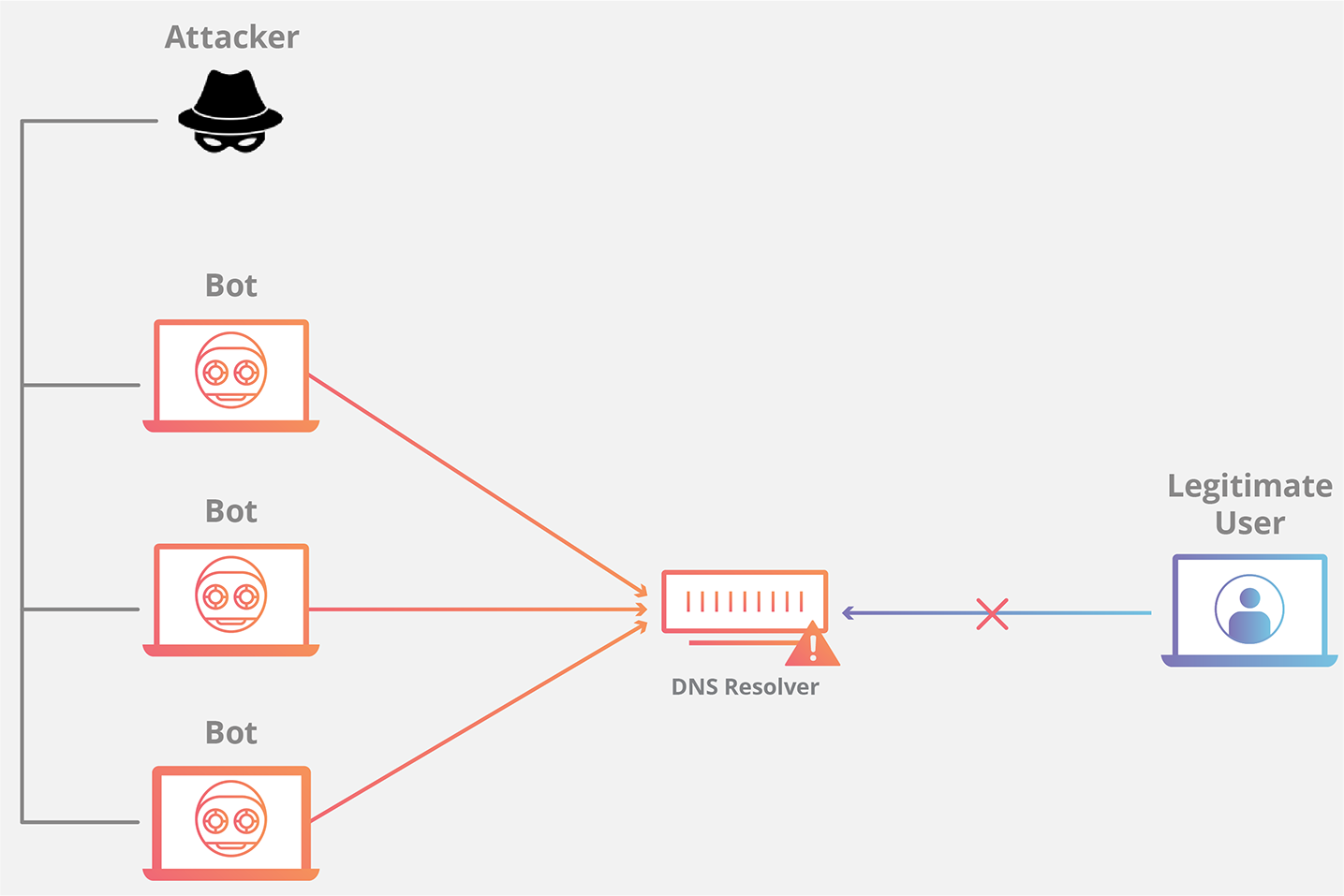
What Is A Dns Flood Dns Flood Ddos Attack Cloudflare

What Is Syn Spoofing Or Tcp Reset Attack
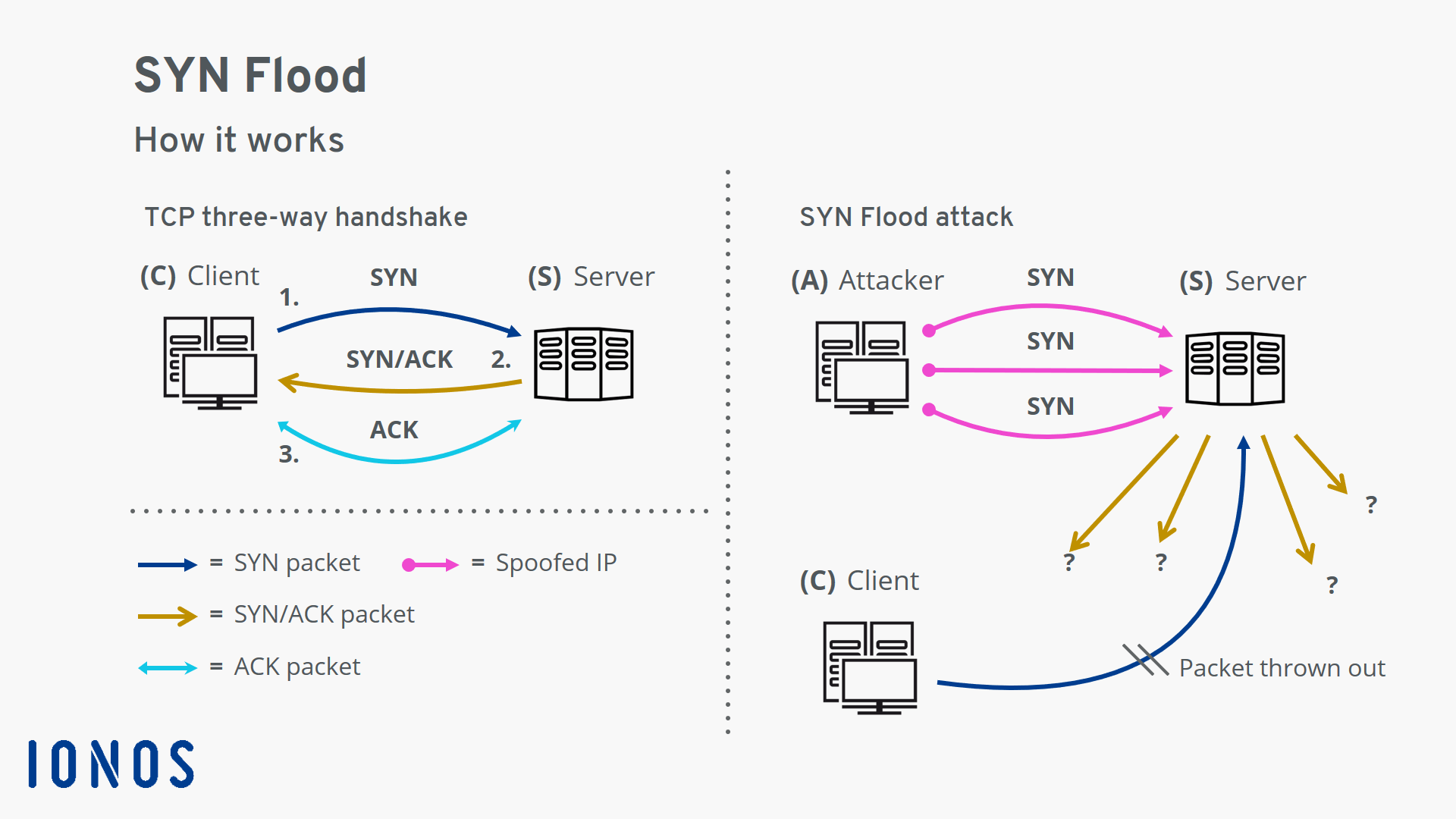
Syn Flood Attack Types Of Attack And Protective Measures Ionos
What Is Syn Synchronize Attack How The Attack Works And How To Prevent The Syn Attack Security Boulevard
What Is A Syn Flood Attack And How To Prevent It Netscout
What Is Syn Synchronize Attack How The Attack Works And How To Prevent The Syn Attack Security Boulevard

02 05 Syn Flood Attacks Youtube
Cisco Networking Vpn Security Routing Catalyst Nexus Switching Virtualization Hyper V Network Monitoring Windows Server Callmanager Free Cisco Lab Linux Tutorials Protocol Analysis Ccna Ccnp Ccie Page 66
What Is An Ack Flood Ddos Attack Types Of Ddos Attacks Cloudflare
How To Prevent A Syn Flood Attack Purplesec
Syn Flood Ddos Attack Cloudflare
How Can You Prevent Ddos Attacks With Log Analysis
Syn Flood Ddos Attack Cloudflare
Syn Flood Ddos Attack Cloudflare

Post a Comment for "How Syn Flood Attack Works"